What is a Vulnerability Scanner?
Finding the vulnerabilities that threat actors exploit is as important to your cybersecurity posture as making sure your front door is locked when no one is home. But many network and security teams are still unaware of all their attack surfaces left unprotected, leaving the door wide open for threat actors to gain access to their infrastructure. Vulnerability scanners can automate this task to collect information and identify potential vulnerabilities quickly and efficiently before they are detected by these actors.
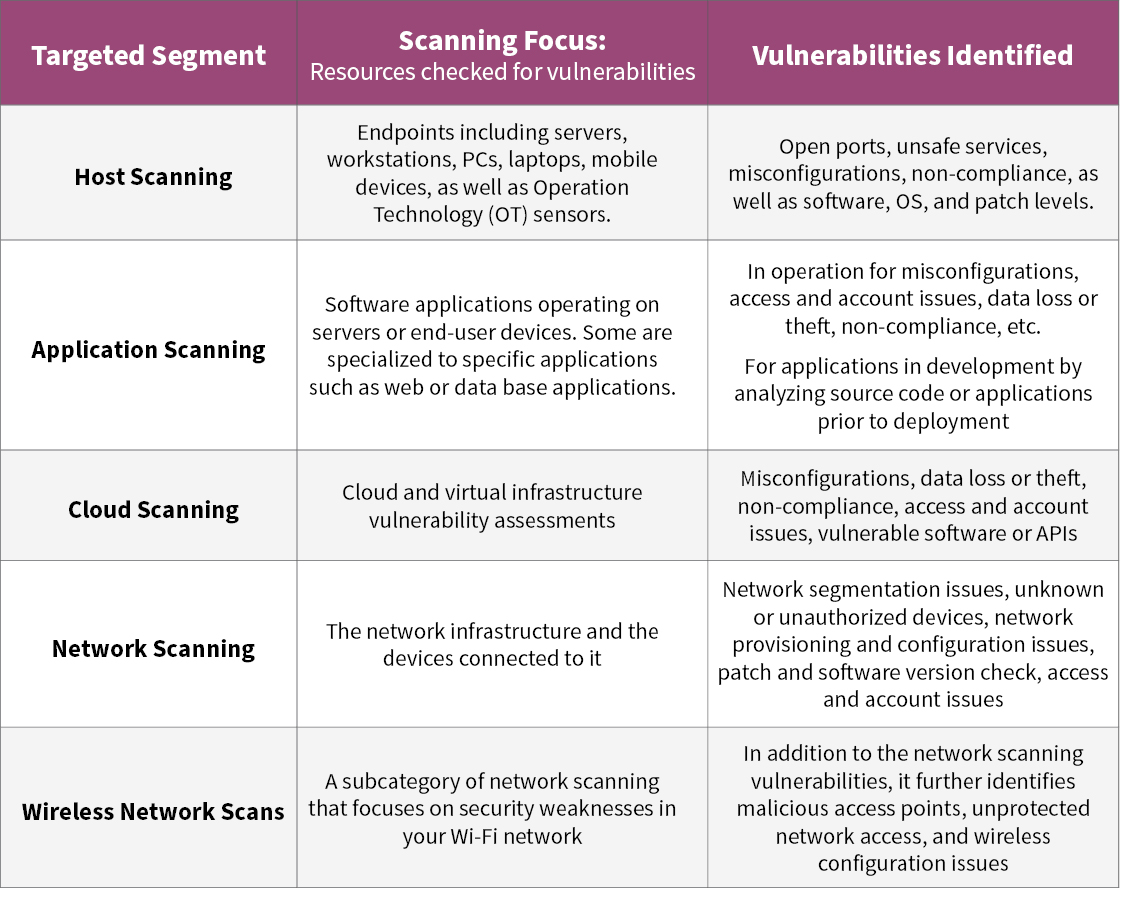
What vulnerability scans are used to identify threats?
Even though many organizations have a dedicated security department, the ever-increasing and sophisticated attacks now require other IT groups, such as network and application teams extend their responsibility into an active role in securing their infrastructure such as applications, the network, and devices. Therefore, vulnerability scanners are often targeting specific segments:
What methods are used to make those assessments?
The above scanners use two primary methods to identify threats: passive and active testing.
Passive testing identifies vulnerabilities or even existing threats by monitoring each system and the interactions it has with other users or devices. This requires obtaining copies of the traffic that these devices generate, which is done either in real-time or captured and then analyzed offline. It has no impact on the end-user or application but gives valuable insight into who communicates with the application or device and what information is exchanged. It can identify any suspicious interaction such as an unusually high communication volume or unusual communication relationships. For instance, it may be a red flag when an HVAC controller communicates directly with a finance server or with a country the company has no business relationship.
Active testing is an intrusive and directive test where the tester actively interacts with the target system, similar to when a threat actor probes a device. Active testing involves:
- Sending login attempts and data requests and analyzing the response
- Performing simple scans to obtain information such as open ports, login attempts, or data requests
- Sending malformed requests or traffic to trigger an error response that may lead to an unwanted response or access to the system
Active testing needs to be applied carefully, as it may create detrimental performance degradations, resets, or even a complete shut-down of the target system if not done carefully.
Success in vulnerability scanning depends on planning and cooperation
As outlined in our previous blog, every vulnerability scan should follow the process of plan – test – assess and remediate – verify and reassess. The planning phase is especially important when vulnerability scanners are used, as they must be properly configured to monitor or target the right devices and applications. This includes the devices and address ranges to scan or monitor, account logins to obtain access to management and configuration information, defining the steps necessary to obtain the desired results, and what information to store and report on. Oftentimes, this may involve more than one tool, such as utilizing management systems that can provide additional background information. This preparation allows for an efficient automation of the scan with limited user intervention while also ensuring that all details are available to assess the vulnerability severity and what counter measures to take.
Cooperation across the various IT organization is vital! Security is no longer just the responsibility of the CIO and his team. It needs to involve other IT operations departments as they are the experts of the infrastructure they manage. They can provide crucial insight on how to scan and assess their infrastructure to identify risks the security team may not have known about.
The overlooked scan – network and wireless scanning
Cooperation between the security team and network operations is essential, as network operations owns the infrastructure that ties all the various services, components, and the third-party providers together. Any vulnerability in the network provides threat actors access to a significant share of the organizations’ applications and server infrastructure and allows them to spy on end-user traffic. With WiFi and physical network access ports reaching out to the corporate perimeter in offices, lobbies, warehouses, and even connections to the public Internet and 3rd party service providers, they sometimes provide easy access for threat actors if not properly secured.
This requires the security team to work closely with network operations to identify vulnerabilities of the network itself and the devices connected to it. Network scanning is a comprehensive approach in
- Discovering all network devices
This includes switches, routers, Wi-Fi access points, firewalls, DNS and DHCP servers and other service providers, and any endpoint connected to the network. This provides an inventory of devices and services that need to be assessed and identifies those that are not authorized and needs to be scanned for additional vulnerabilities. - Mapping the entire topology of every device connected to the network
This provides a comprehensive view on where devices are located and what other parts of the network can be reached. As such, this is especially important as network segmentation is critical to restrict lateral movement of threat actors, preventing them from moving freely around the network into more sensitive areas. - Testing the inventory of all active hardware and software in the network infrastructure. This discovers provisioning and configuration issues, unauthorized access to devices through misconfigured or compromised logins, outdated or unpatched software, or network segmentation issues.
- Wireless network scanning
This includes all the above, but further specializes in identifying wireless security weaknesses. As wireless networks can extend far beyond your physical property boundaries, they are an easy target for threat actors to explore. Wireless network scans test for malicious or unauthorized access points, identifying which channels and bands are utilized by any connected device to identify any unprotected or unauthorized users. It identifies wireless configuration issues that may create opportunities for threat actors to connect from outside your physical property through WiFi networks that may not be properly secured or broadcasting their SSID for easier discovery.
In Summary
Vulnerability scans require cooperation between security teams and the infrastructure domain experts and using the proper tools for the target under test or investigation. This should especially include the network, as it reaches across your entire infrastructure to any device of interest for the threat actor. Proper upfront planning ensures an effective scan with all the details needed to assess the vulnerability severity and to determine appropriate counter measures.

