Advantages of WPA3 for WiFi Security
This is the second blog in a series of WiFi 6 and the new spectrum. Read blog 1; Designing for 6Hz Channels.
Security has been a cornerstone topic in the past few years as security breaches intensify. So, it’s only fitting that as we start to talk more about WiFi 6/6E and 6GHz, we talk about security and its impact on how we secure our networks. With WiFi 6/6E we have the opportunity to force the use of enhanced security protocols, such as WPA3. Let’s look at WPA and why we want to migrate to WPA3 with 6GHz.
What is WPA or WiFi Protected Access
WiFi Protected Access, or WPA, is the foundation for creating a secure Wireless connection. The WiFi Alliance originally developed it in 2003 under the 802.11i amendment to replace the aging Wired Equivalent Privacy or WEP. Without getting too deep into things, the process we are working on is creating a set of encryption keys that are used to send a message over the radio waves securely. With WEP, a 64 or 128-bit key would be created and shared manually across all the devices you wanted to connect to the Wireless network. The key never changed. It was always the same. Because of this, anyone who knew the key could a) connect to the Wireless network and b) decrypt other devices’ traffic. A little disturbing when you think about it!
To improve security, WPA removed the process of sharing the encryption key and exchanged it for sharing of a passphrase or known set of credentials, referred to as Personal (PSK) or Enterprise. The exact strength of encryption keys created is the same. It doesn’t matter if you use Personal or Enterprise. Let’s look at the key hierarchy; then, we’ll review the keys.
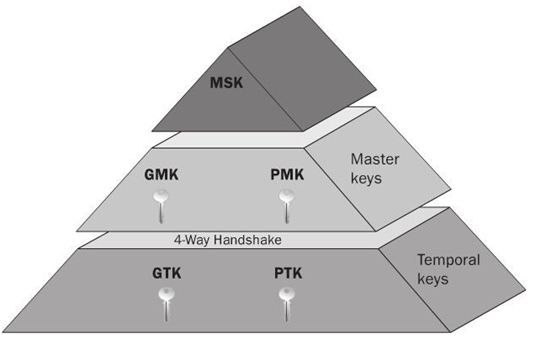
At the top of the pyramid of keys is the Master Session Key or MSK. The MSK is used to derive the Pairwise Master Key, or PMK, through either the pre-shared key (PSK) or EAP method (RADIUS authentication). The strength of the security comes from how strong the PSK is, or the EAP credentials used. It doesn’t matter if you use an eight-character or 32-character PSK, EAP-PEAP username/password, or EAP-TLS certificates. It will always become a 256bit key value and is the basis for all other keys in the process. Creating the encryption keys is called the “Four Way Handshake.”
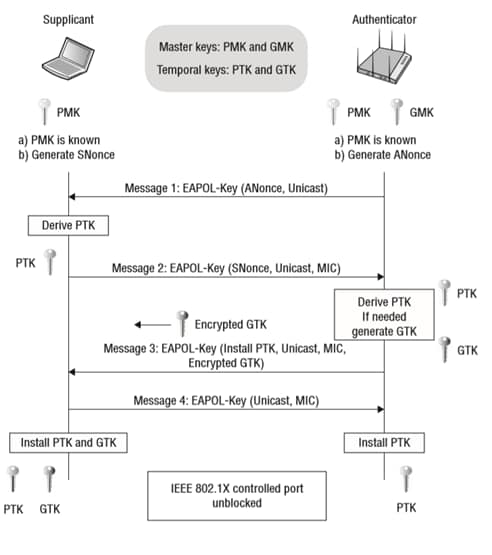
This Four Way Handshake allows us to create a working set of encryption keys without actually sharing them, utilizing the process of exchanging smaller bits of data during each step. Because this process happens over the air, someone can intercept it, but you need to know the value used for the MSK/PMK. With WPA, Temporal Key Integrity Protocol (TKIP) encryption is used and is easily compromised by brute force to retrieve the PSK. WPA2 utilizes Advanced Encryption Standard (AES) and Cipher-block Chaining Message authentication Protocol (CCMP). While the encryption behind the WPA2 process is more challenging, the Four Way Handshake can be compromised and result in denial-of-service attacks against clients and stations.
WPA3 strengthens WiFi security
WPA3 strengthens WiFi security by enabling a more robust but simple authentication process. One of the ways it does this is by requiring what is called Protected Management Frames (PMF). PMF is not a new technology and has been an optional feature of Wireless devices for years. For the first time with WPA3 it is required. PMF ensures that other devices cannot force clients to de-authenticate. For example, if I was an attacker trying to breach a network or device, I needed to capture the Four Way Handshake process to determine the encryption keys used for that session. To do this, I have two options: a) sit around and wait for them to connect/reconnect, or b) force them to disconnect so they will reconnect. Attackers will opt for option b and craft a de-authentication frame directed towards the client device. Upon receiving this frame, the client has to listen to it and do what it says; there are no checks and balances to ensure that it is from the AP. PMF adds a layer on top of this that creates checks and balances.
The second key feature of WPA3 is it allows for more robust password-based authentication even if my password is “password.” This process is enabled through Simultaneous Authentication of Equals (SAE). Through the SAE exchange, we learn that each side, client and network, possess the same password and can establish a strong key used in the Authenticated Mesh Peering Exchange (AMPE) to protect the traffic. We won’t be going into great depth about the SAE process, but we encourage you to look at the Diffie-Hellman key exchange process if you are curious. The SAE process combined with PMF fixes the man-in-the-middle attack issue of forcing a de-authentication and capturing the Four Way Handshake resulting in a potentially insecure connection.
WPA3 and 6GHz
For the first time since the introduction of 802.11a and the 5GHz band we have the opportunity to avoid supporting outdated legacy protocols as well on WiFi 6/6E. As you consider deploying 6GHz networks you will have to prepare to support WPA3 as it is required for 6GHz networks. You should deploy a new network name (SSID) for your 6GHz devices, which can also be enabled on 2.4GHz/5GHz if you are not deploying 6GHz everywhere and only deploying it in high-density areas. As you deploy WiFi 6/6E devices, configure them for your new, faster, more secure network leaving your WiFi 5 network for legacy devices.
Final Thoughts
If you have attended one of my courses or seen my other training materials, you will remember we discussed the concept of too many networks causing congestion. This statement is true and accurate, so why am I advocating for adding another network? It’s simple: forced migration at your pace. It doesn’t necessarily make sense to potentially disturb hundreds of devices by switching them to WPA3, increasing support tickets. As new devices are introduced, if they are capable of WPA3, it does make sense to put them on this new network even if they don’t support 6GHz. Management frame overhead on WiFi 6 is minimal; I consider it a wash when moving devices between networks on the same frequency, in this case, 5GHz. Over time your legacy WPA2 network will become much like the WPA networks of the years past, lightly used and ready for decommissioning.




